Corporate Email Compatible with Administrative Software This prevents your operations from depending on whether they've arrived. Therefore, if your administrative system sends invoices, statements, notices, reports, or confirmations, it's best to treat email as an operational component: measurable, secure, and diagnosable. Furthermore, when email is well integrated, the team stops manually resending, reduces complaints, and consequently maintains traceability.
Corporate Email Integrable with Administrative Software: What Your Operation Should Require
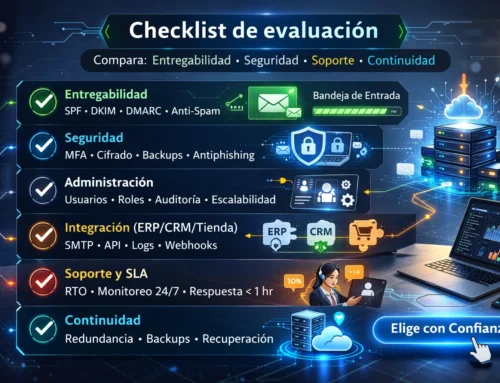
When someone asks for "corporate email," they often think of mailboxes. However, administrative software needs something more specific: a stable outgoing channel (SMTP), aligned authentication (DNS), and support that can provide evidence explaining why a message bounced or went to spam. In other words, it's not enough for it to "send today"; what matters is that it maintains consistency when volume increases, when recipient policies change, or when the team grows.
For this reason, before comparing "plans," define the desired outcome: that the system sends emails using TLS, that the domain has SPF/DKIM/DMARC configured, and that queue, bounce, and alert monitoring is in place. Furthermore, it's advisable to separate system email from user email, because this way, a broken password or a misconfigured client won't disrupt the software's delivery.
If you want to review a proven approach to ERP operations, you can read the guide from email provider for enterprise ERP and reuse the same criteria for your administrative software.
Within this context, if you want to validate your case without buying "blindly", you can start here: 👉 We've set up your email address, ready for you to start using it.so that integration is proven with evidence and not with assumptions.
What does it mean to integrate email with your administrative software?

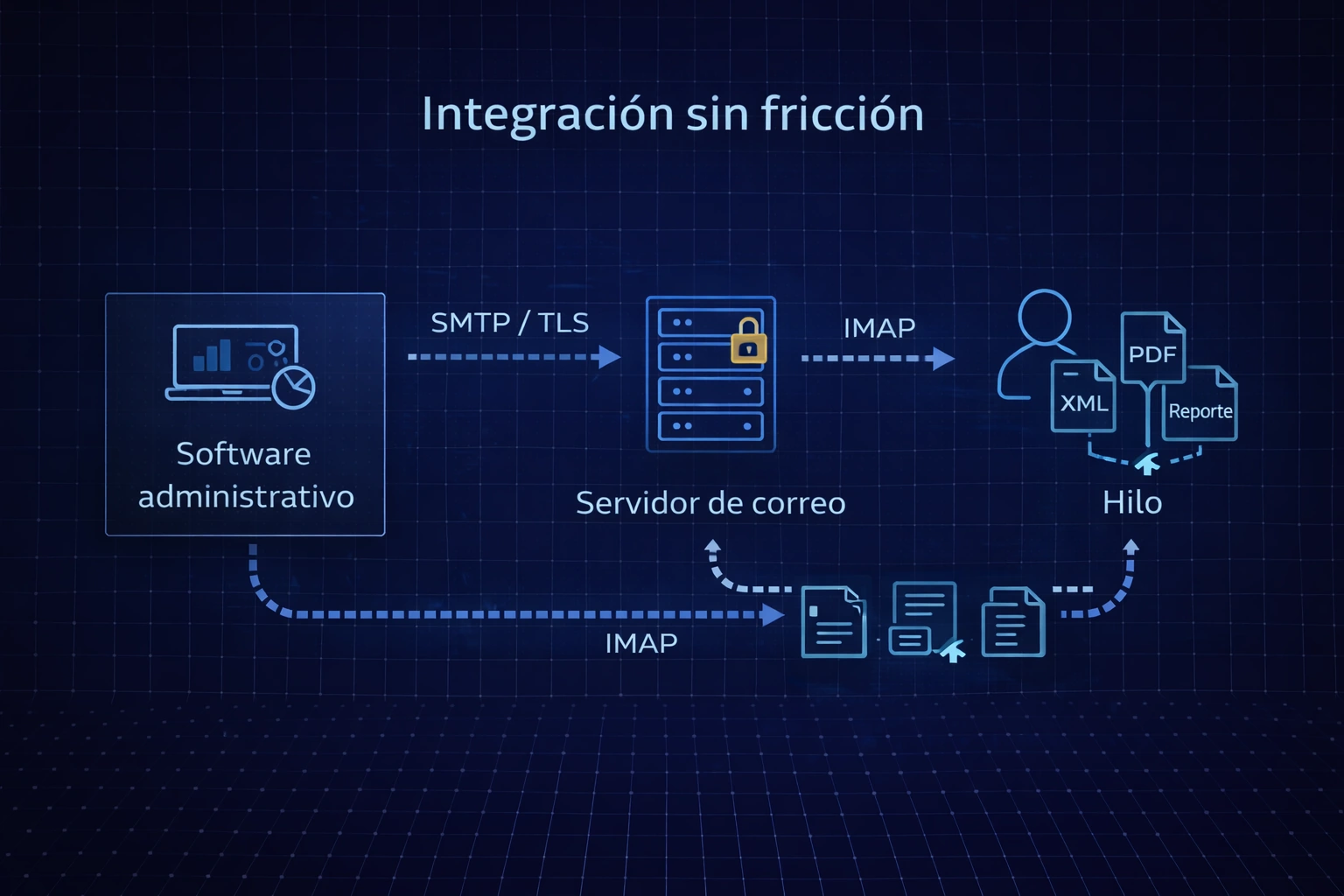
Frictionless shipping and registration
Integration, in practice, means three things. First, that the system can authenticate and send via SMTP without blocking. Second, that recipients trust your domain (DNS authentication and reputation). Finally, that your team can track what happened if something goes wrong (headers, logs, and queues).
Furthermore, integration implies operational order: senders by role (e.g., billing@, collections@, notices@), responsible parties, and change control. Consequently, email ceases to be "someone's issue" and becomes a process-driven component.
Technical requirements for a frictionless, integrable corporate email

Decide based on evidence, not price.
For the integration to be stable, it is advisable to validate minimum requirements, because otherwise the problem appears "intermittent", which is the worst type of problem.
Transport and encryption
-
authenticated SMTP.
-
TLS successfully negotiated (valid certificate and accepted encryption).
-
Standard port that does not conflict with firewalls (frequently 587 with STARTTLS).
Reception and traceability
-
IMAP stable if your system needs to read replies or archive messages.
-
Mailboxes by role and clear rules of use.
-
Evidence record (full headers and, where applicable, server logs).
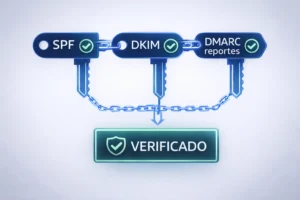
DNS Authentication
-
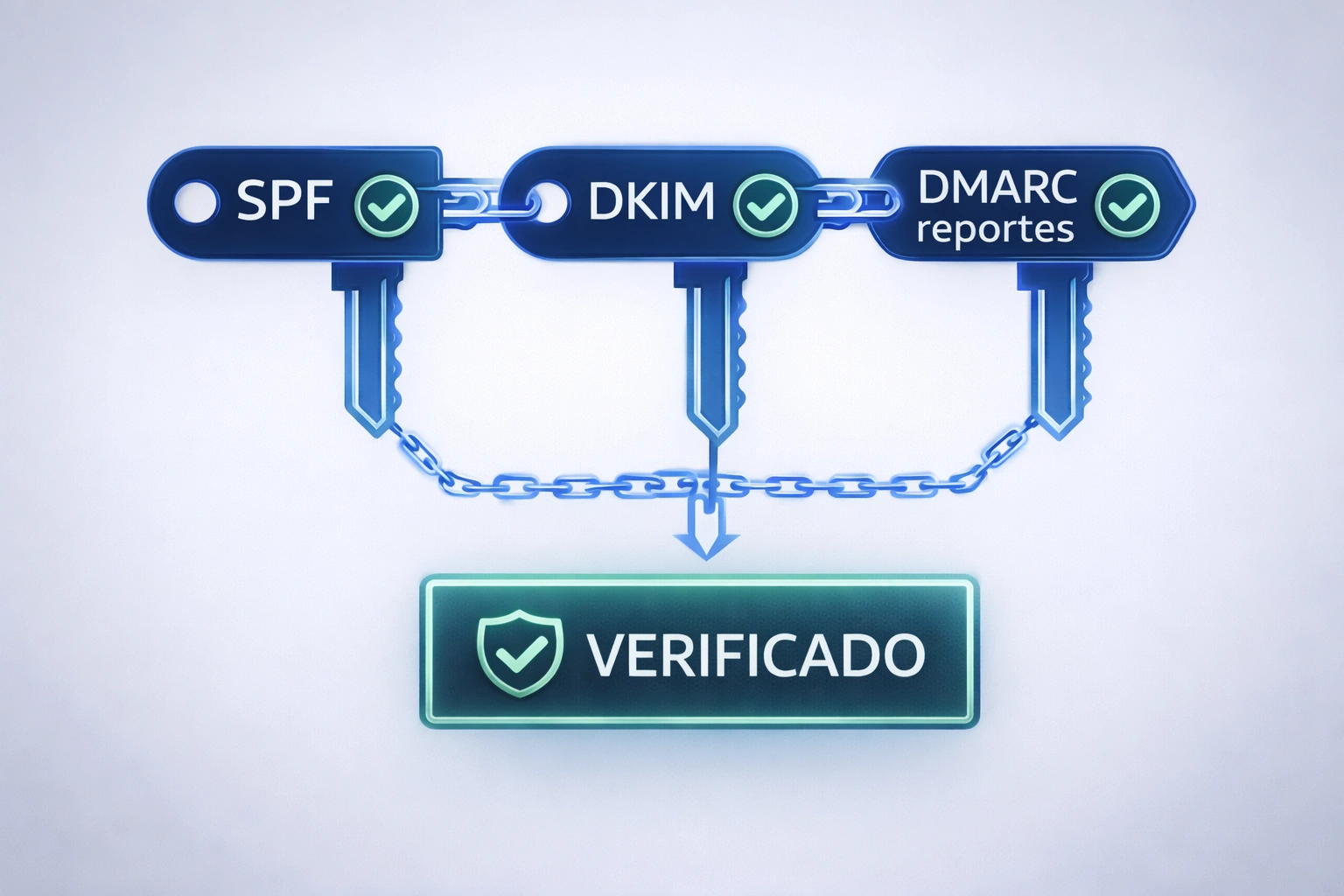
SPF, DKIM and DMARC aligned with the sender's visible domain.
-
Real validation (not just "it's already published"), checking results in headers.
Therefore, if your provider cannot demonstrate these points, the operational risk remains. Conversely, when they are met, the email behaves predictably.
If you're interested in comparing service levels (managed email, monitoring, support, and escalation), check out the server plans for business emailAdditionally, if you want that review applied to your specific case, here's another direct option: 👉 Leave your email in the hands of experts.
Secure SMTP and TLS: The outbound channel your system needs
Fewer bounces and more commitment
Most "mysterious" failures originate from this source: blocked ports, poorly negotiated TLS, or credentials changed without oversight. Therefore, standardization is advisable. This means defining a transmission method that works across corporate networks, encrypts data in transit, and uses controlled credentials.
In this point, Corporate Email Compatible with Administrative Software This means the outbound channel doesn't depend on "someone's computer," but on a service that is validated and maintained. Furthermore, when the channel is consistent, you can analyze bounces using SMTP code and correct them precisely, instead of relying on trial and error.
IMAP, mailboxes by role, and business continuity
If your operation requires responses to reach the correct department, or if you need departmental organization, role-based mailboxes solve real problems. For example, collections@ and billing@ prevent a process from depending on a single personal inbox. Furthermore, the history is maintained even if the responsible party changes.
Similarly, if your administrative software "reads" incoming emails (depending on the system), IMAP must be stable. Therefore, it's advisable to protect credentials, document changes, and periodically validate connectivity. Consequently, you reduce the typical silent failure where the system stops logging messages and no one notices until a complaint is filed.
SPF, DKIM, and DMARC authentication for sustainable deliverability
Even though the email is sent, the recipient decides whether to accept, downgrade, or reject it. Therefore, SPF/DKIM/DMARC are the layers that transform sending into delivery. Furthermore, DMARC provides reports, allowing for data-driven corrections rather than relying on intuition.
In operation, Corporate Email Compatible with Administrative Software This also means your domain isn't damaged by spoofing or unauthorized sources. Consequently, your reputation is protected, and system messages are delivered more consistently.
For further reference on how this is expressed in a "real support" service, you can review this external guide: Business email with real support: 2025 pricingThe usefulness here is understanding what to include and what to require, not just "how much it costs".
Attachments, XML/PDF and limits: tests that prevent surprises
In administrative software, attachments matter. That's why a serious integration tests with real files: PDFs, XML files, reports, and typical file sizes. It also validates what happens with anti-malware filters, vendor limits, and recipient policies.
Without testing, the usual scenario unfolds: small messages may arrive, but actual attachments fail at critical moments. Consequently, the team ends up resending via WhatsApp, uploading to Drive, or repeating processes. Therefore, evidence-based testing is not an "extra," but rather an integral part of operational control.
In this section, the central idea reappears: Corporate Email Compatible with Administrative Software It is the one that is validated with real cases, not with a "test email" that does not represent your operation.
Monitoring, queues and logging: support that makes a difference
The value of monitoring is simple: it lets you know sooner. If queues are growing, there's a block; if bounce rates are rising, there's a reputation or DNS issue; if there are DKIM alerts, something has changed. Therefore, monitoring reduces wasted time and, moreover, accelerates fixes with evidence.
In this stage, Corporate Email Compatible with Administrative Software It also includes support that reads logs and headers, and can tell you "what happened" and "what changed." Consequently, the team no longer has to constantly respond to emergencies.
If you want to speed up diagnosis and implement the right plan based on your system and volume, you can start: 👉 Complete Solution: Email + Support.
How to choose a provider: signs that you need a managed service
There are clear signs. For example: frequent outages, emails going to spam, bouncing attachments, dependence on the end of the month, or a complete lack of evidence when something goes wrong. Furthermore, if the domain is modified without authorization (DNS), the problem recurs.
In these cases, a managed service is usually the better option because it includes monitoring, logging, and escalation support. Therefore, instead of "reboot and test," you get data-driven diagnosis and resolution.
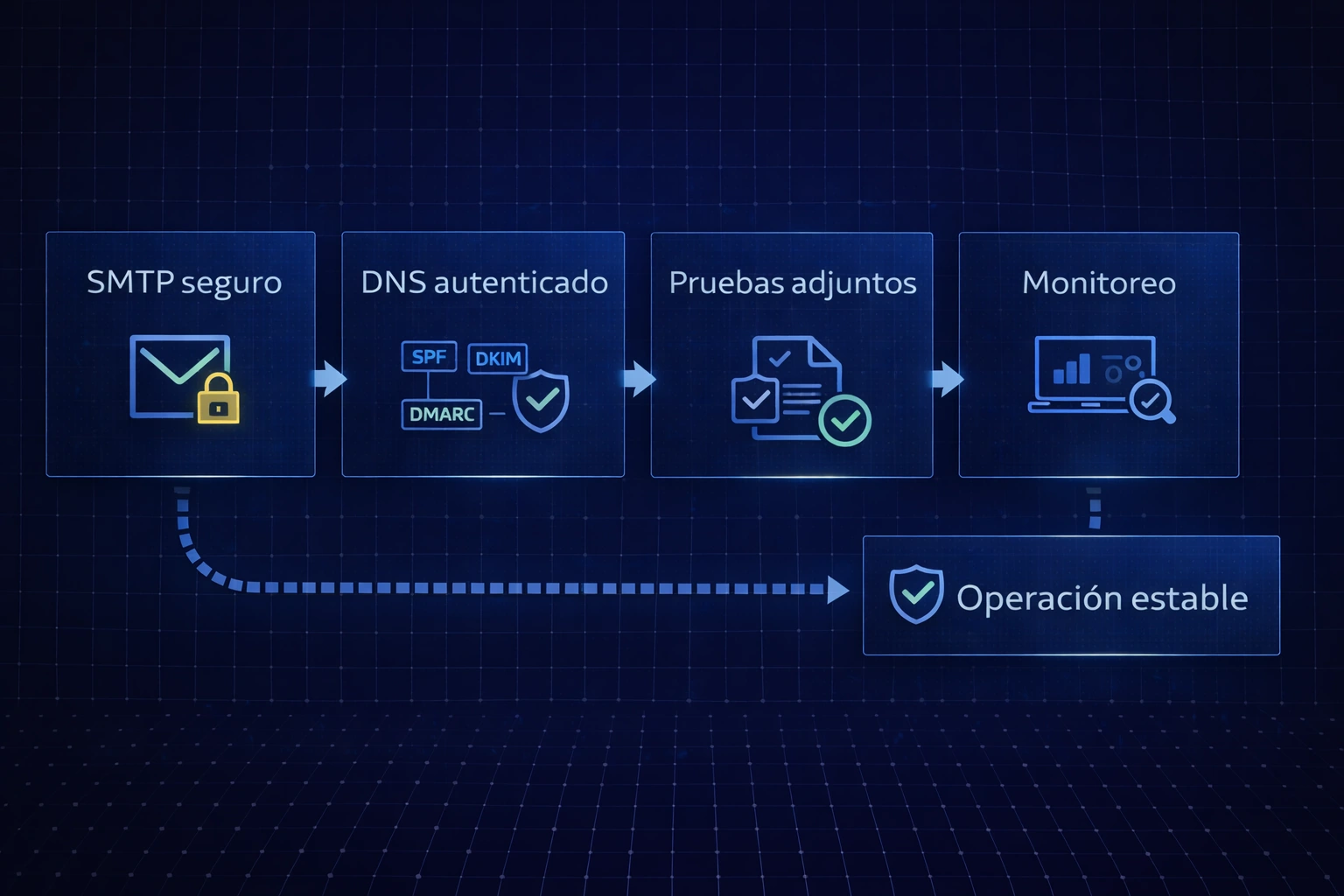
5-step implementation plan

Timely tracking and documentation
To operate without surprises, a short and repeatable plan is advisable:
-
Validate SMTP with TLS and standard port, with real tests.
-
Align SPF/DKIM/DMARC and check results in headers.
-
Define senders by role and separate system mail vs. user mail.
-
Test real attachments (PDF/XML/reports) and typical volumes.
-
Activate queue monitoring/alerts and change log.
By implementing this plan, Corporate Email Compatible with Administrative Software It ceases to be a phrase and becomes a stable operation.
To conclude with an actionable step, if you want to review your case and choose the right plan with support in Mexico: 👉 Talk to a Business Email Specialist.
FAQs: Frequently Asked Questions
What makes a corporate email "integrable" for administrative software?
The system must be able to send via SMTP with TLS, the domain must be authenticated with SPF/DKIM/DMARC, and there must be evidence (headers/logs) for diagnosis.
Why does my system "send" but the client doesn't receive?
Because sending is not delivery. Therefore, if SPF/DKIM/DMARC are not aligned, or if the reputation is degraded, the recipient may reject the email or mark it as spam.
How many senders should I use for administrative software?
Senders by role (billing, collections, notices) are advisable because, in this way, you maintain continuity and control, even with staff turnover.
What should I try before changing my email provider?
Sending to Gmail/Outlook/corporate accounts, checking headers, testing with real attachments, and validating queues/alerts. Consequently, you reduce surprises.
What role does DMARC play in daily operations?
In addition to policy, DMARC provides reporting. Therefore, it allows you to detect unauthorized sources and protect your reputation.
How do I know if the problem is my network or the provider?
It is confirmed by the type of error: if it is connection/port/TLS, it is usually network or local configuration; if it is rejection due to policy or reputation, it is usually authentication or domain.
When is a managed service appropriate?
When email supports critical processes, experiences interruptions, or requires evidence-based support and escalation, a managed service reduces risk.
What does a good "data-enabled" email support service include?
Reading headers, analyzing SMTP codes, reviewing queues and, when applicable, server logs; in addition, change log.
How can I ensure that Corporate Email that integrates with Administrative Software remains stable over time?
With monitoring, change control, periodic authentication validations, and testing when you change DNS, users, or volume.



 We provide the service you need, click here
We provide the service you need, click here